The malware analyzed by Cisco Talos security experts hides in Microsoft Word documents and targets government offices of countries belonging to NATO. Cisco suspects government agencies as the originator.
The rather unusual malware analyzed by the security experts at Cisco’s Talos Group hides in Microsoft Word documents and targets government offices of countries belonging to NATO. The malware is intended to spy on state secrets. The campaign was carried out between Christmas and New Year. There is currently nothing to suggest that government agencies have been infected with the malware.
Seemingly harmless document with a sophisticated infection routine. The Cisco Talos team suspects government agencies are behind the malware.
Since the specialists found numerous sophisticated components in the digital malware, this suggests that it is not a question of conventional malware, but that government agencies could have developed it.
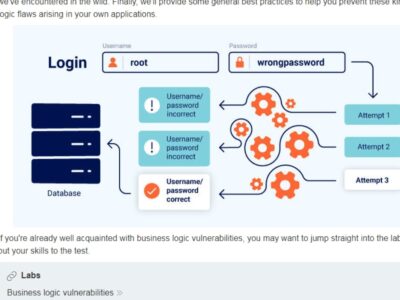
In the analysis titled ‘Matryoshka Doll Reconnaissance Framework,’ experts noted that this malware has various unusual features. The malware can circumvent sandbox security solutions and, by importing garbage data, ensures that security technologies are crashed.
The malicious document also has a sequence of embedded objects. These trigger the actual payload of the malware over several stages. It then connects to a command and control server. In addition to various other information, the malware then reads the operating system and Adobe Flash version and reports this to the C&C server.
“The analysis of the Microsoft Office document shows a very sophisticated workflow of infection. The real purpose of the document is to spy on the victim to bypass communication with a sandbox or a security analyst’s machines. Second, Adobe Flash gets the payload and an exploit for Adobe Flash, which loads and runs,” explains Cisco’s Talos team.
Cisco speaks of the Matryoshka Doll Reconnaissance Framework, which defends itself against access by security solutions via various embedded objects.
The Word file examined is an RTF document in which an OLE object is initially embedded. And in this OLE object, there is, in turn, an Adobe Flash object. A binary is then extracted via ActionScript, an Adobe Flash object compressed with XOR and zlib. Only this second Adobe Flash object is the actual payload of the malware, which then creates an HTTP connection with the C&C server.
From the point of view of the attackers, this approach is very clever, and it is said because the actual exploit is not embedded in the document and cannot be detected by an antivirus program. According to the authors, the attackers set up a minimalist but very efficient framework, which can also be changed when used.
It is also interesting that the actual payload is issued with large amounts of junk data. The attackers want to cause resource problems in the security systems. This is primarily intended to make it impossible to examine the malware. The security experts only conclude from the file name of the manipulated document that this malware was primarily intended to scout out NATO members.





















Comments